How to Install Antivirus on a VPS or Dedicated Server
Want to keep your server safe from online threats? In this easy-to-follow guide, we'll show you how to install antivirus software on a VPS or Dedicated server and set up two popular antivirus options, ClamAV and ImunifyAV, to help you lock down your server and keep those digital bugs away.
There are two main types of virus scanning on VPS and Dedicated servers:
Installing and using ClamAV
First, you will need to be able to log into your WHM.
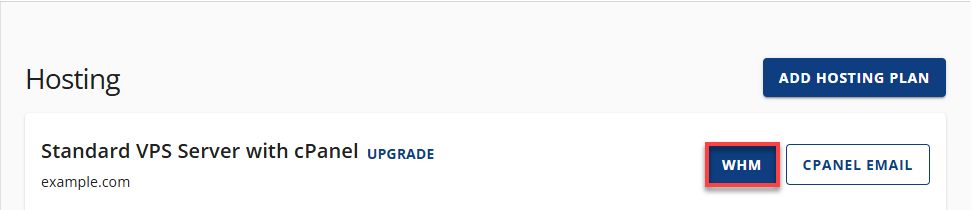
- Log in to your Bluehost Portal.
- Click Hosting in the left-hand menu.
- In the hosting details page, click the WHM button.
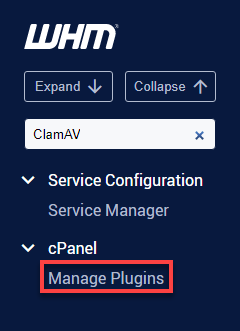
- Type ClamAV in the search bar in the top left-hand corner, then click on the Manage Plugins link.
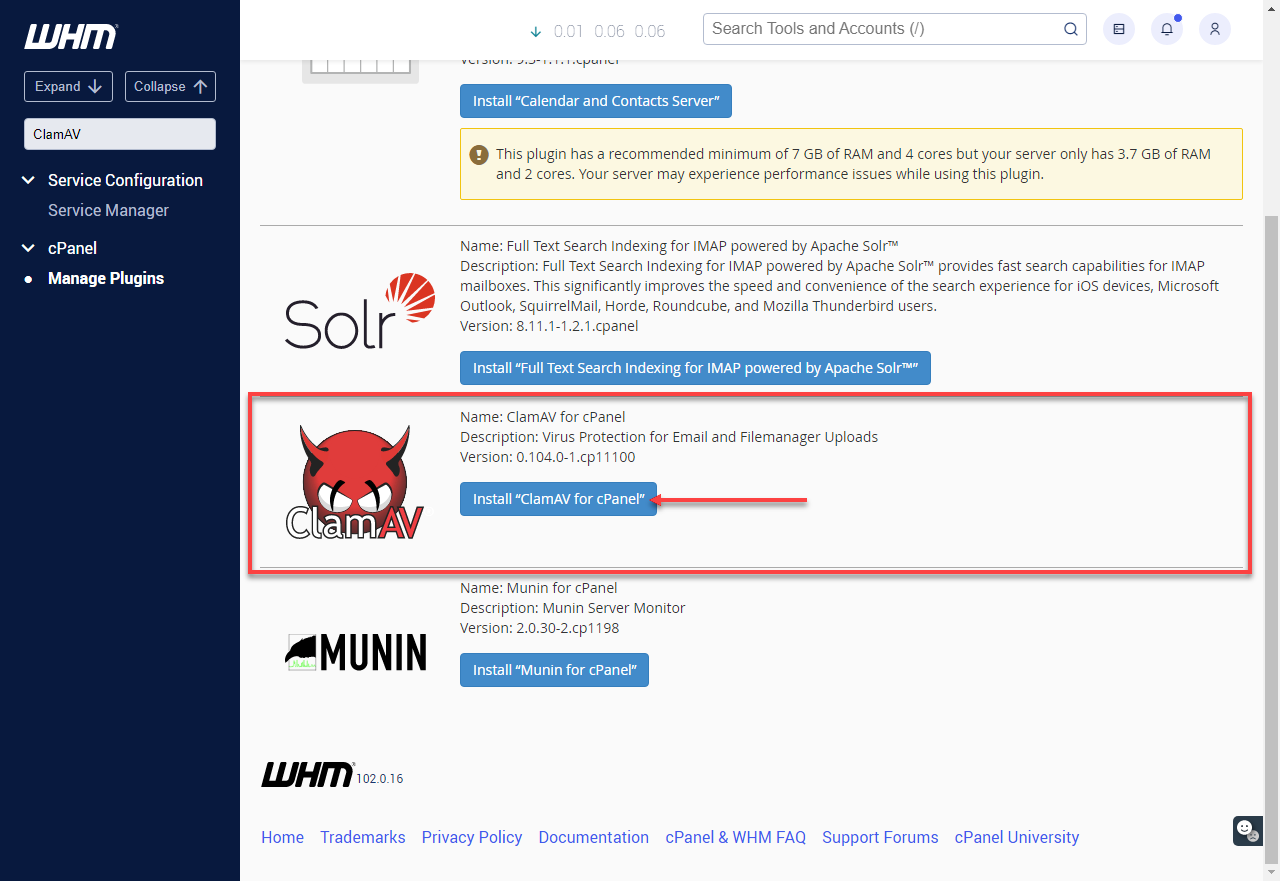
- Click on the Install ClamAV for cPanel.
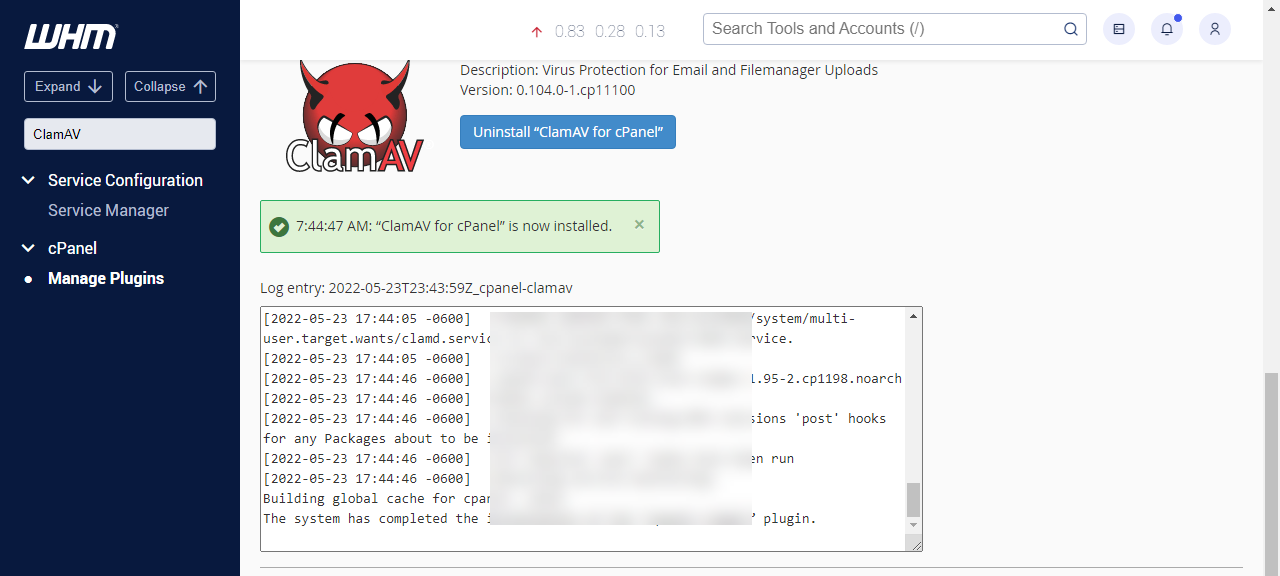
- Once the installation is complete, you will see the ClamAV for cPanel is now installed message.
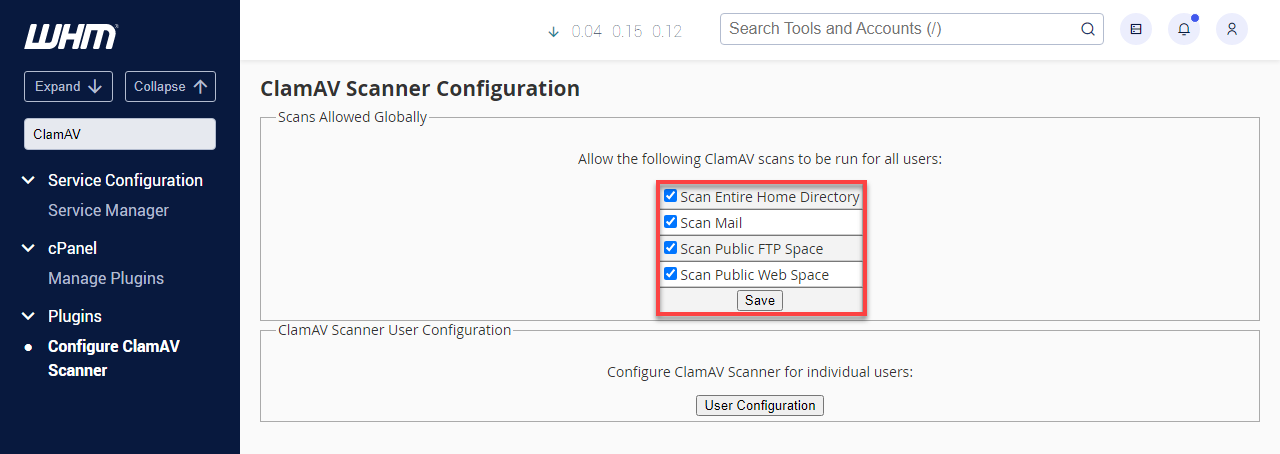
- Refresh the WHM panel and perform another search for ClamAV using the search bar. Click on Configure ClamAV Scanner, and make sure all boxes are checked.
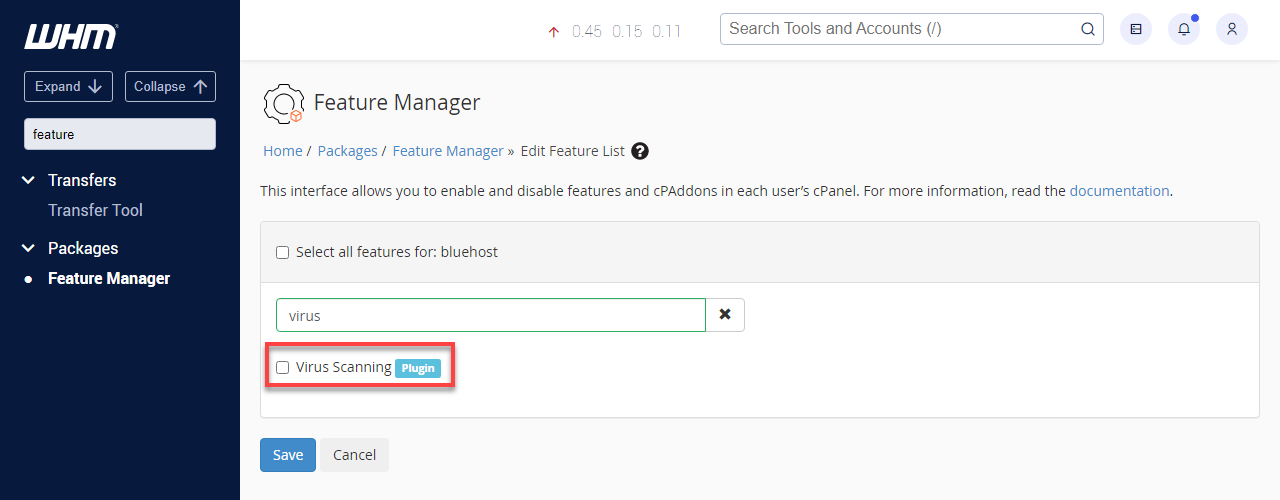
- Search WHM for a feature, and click on the Feature Manager. Choose Bluehost from the Manage feature list, then click edit.
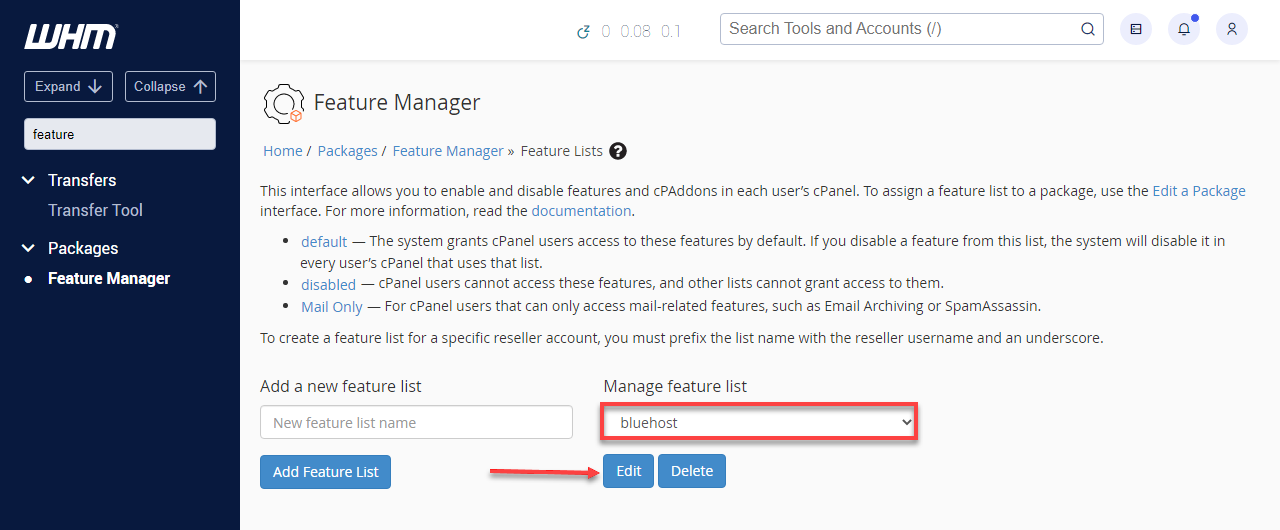
- Enable Virus Scanning, and click Save. You can find this quickly by searching for a virus on the Feature Manager page.
- Now that ClamAV is installed, you can manually run a scan from your server's command line as the root user.
- For more information on using SSH, please see SSH Access.
- Be sure to replace the $user with your cPanel username in the command below:
root@server [~]# /usr/local/cpanel/3rdparty/bin/clamdscan -i /home/$user/ - Once the scan is complete, you will receive an output of flagged files and a scan summary. You can use this to help you clean up your cPanel account.
You can uninstall ClamAV under the Manage Plugins section of your WHM panel.
Installing and using ImunifyAV
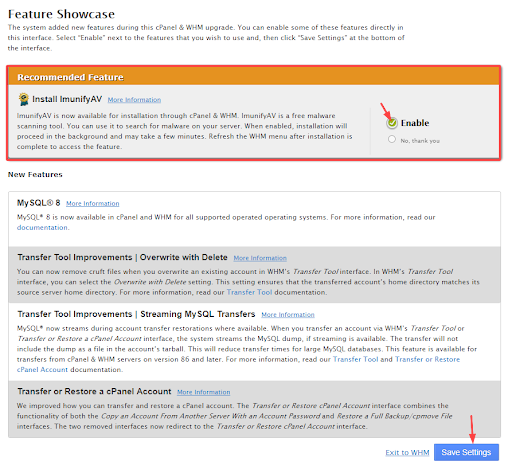
Imunify360 is a new feature that gets shipped with cPanel starting in cPanel 88. Below are the steps to install and use this new malware scanner.
- When you upgrade to cPanel 88, you will see the feature showcase in the Feature Showcase. If you want to install ImunifyAV, make sure Enable is selected, then click the Save button at the bottom.
- If the Feature Showcase does not appear when logging into WHM, you can install ImunifyAV manually via SSH.
root@server [~]# wget https://repo.imunify360.cloudlinux.com/defence360/imav-deploy.sh
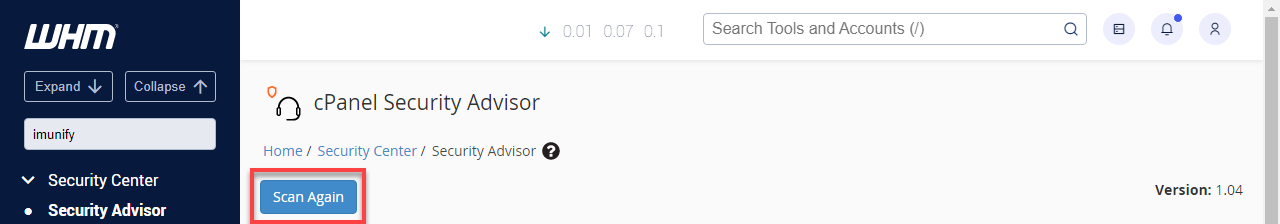
root@server [~]# bash imav-deploy.sh - Once the installation process has begun, wait about 5-10 minutes for the installation to finish. After completing it, visit the ImunifyAV section in your WHM panel by typing imunify in the search bar and clicking Security Advisor.
- From the ImunifyAV screen, click the actions button next to your cPanel account, and click "Scan for Malware." When it is done, it will give you results.
- You can select all accounts and scan them simultaneously if you have multiple accounts.
root@server [~]# bash imav-deploy.sh --uninstallSuppose you have deleted the imav-deploy.sh, you can re-download it first:
root@server [~]# wget https://repo.imunify360.cloudlinux.com/defence360/imav-deploy.shSummary
If files show up on any of the malware scans, please note that some of the files might be vital to the functionality of your site and only contain snippets of malicious code that have been injected. You will want to work to remove the malicious code without deleting the file. Other files might be wholly malicious and should be deleted.
If you need assistance with removing malware, we recommend reaching out to our malware scanning partner, SiteLock. SiteLock also has plans that include a content delivery network (CDN) and a web application firewall (WAF) that aid in protecting against malicious attacks.
You've now learned how to install antivirus software on your VPS or dedicated server. Don't forget to keep your software updated and run regular scans to ensure your server stays protected. A little maintenance goes a long way in keeping your data safe and sound!
If you need further assistance, Bluehost Chat Support is available 24 hours a day, 7days a week while Bluehost Phone Support is available 7 days a week from 7 am-12 midnight EST.
- Chat Support - While on our website, you should see a CHAT bubble in the bottom right-hand corner of the page. Click anywhere on the bubble to begin a chat session.
- Phone Support -
- US: 888-401-4678
- International: +1 801-765-9400
You may also refer to our Knowledge Base articles to help answer common questions and guide you through various setup, configuration, and troubleshooting steps.