Key highlights
- Understand the whitelist IP address meaning and how IP whitelisting enforces a default-deny security model that allows access only from trusted IP addresses.
- Learn how to whitelist IP address rules across firewalls, applications, databases and hosting platforms to protect systems from unauthorized network access.
- Explore when to use IP whitelisting and IP range whitelisting for administrative access, API security, database connections and internal network controls.
- Know how IP address changes, dynamic IPs, IPv4 and IPv6 differences and formatting errors can affect a whitelist IP address and how to troubleshoot blocked access.
- Uncover best practices from network security consulting by combining IP whitelisting with authentication, monitoring and layered security controls for long-term protection.
Imagine leaving the front door of your office unlocked and hoping only the right people walk in. That is what open network access looks like without controls. IP address whitelisting changes that by allowing only known and trusted sources through the door while everyone else is turned away.
When you whitelist IP address access, you create an approved list of IP addresses that can connect to your systems, networks or applications. Any address not on that list is blocked by default. This approach reduces exposure and helps protect sensitive resources from unauthorized access attempts.
Understanding what is IP whitelisting and the whitelist IP address meaning is essential for building reliable access controls. Knowing how to correctly whitelist IP address rules enables you to apply this protection across servers, databases, APIs and applications while supporting stronger, more intentional network security decisions.
What does it mean to whitelist IP address?
The whitelist IP address refers to a security practice in which you explicitly allow specific IP addresses to access a system, service or network resource. Think of it as a guest list for an exclusive event – only approved addresses get through.
When you implement IP whitelisting, your system automatically denies access to any IP address not on the approved list. This creates a default-deny security model where access must be explicitly granted rather than blocked.
IP address whitelisting works at different network layers. Firewalls can whitelist addresses at the network level. Applications can implement whitelisting at the software level. Web services can restrict access based on client IP addresses.
The key difference between allowing trusted IPs and blocking unknown traffic lies in the approach. Whitelisting starts with “deny all” and adds exceptions. This provides stronger security but requires more management, as you must approve each legitimate IP address. Before those exceptions can be created, you first need to identify the IP address that will be whitelisted.
How to find your IP address before whitelisting
Before adding any entry to a whitelist, you need to identify the correct IP address that external systems will recognize and allow. The steps below help ensure you capture the right address and avoid common whitelisting errors.
Prepare for the next configuration step: With these access decisions in place, understand how IP whitelisting is applied when securing database connections.
Identify your public IP address: Visit a service like whatismyipaddress.com or use command-line tools. Your public IP address is what external systems see when you connect.
Distinguish between internal and external IP addresses: Internal addresses such as 192.168.1.100 work only within local networks. External systems require your public IP address for whitelisting.
Confirm the correct IP address before whitelisting: Test connectivity from the intended source to ensure the correct IP address is being added. Incorrect entries will result in continued access denials.
Decide between a single IP address or an IP range: Organizations with multiple users may need subnet-based whitelisting rather than individual IP addresses.
With these access decisions in place, the next step is understanding how IP whitelisting is applied when securing database connections.
How to whitelist IP address for secure database connections
To whitelist an IP address for MySQL access, begin by logging into your Bluehost Account Manager. Once you’re logged in, follow these steps.
1. Log in to your Bluehost Account Manager.
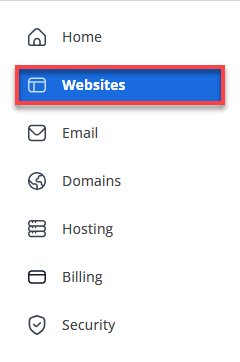
2. In the left-hand menu, click Websites.
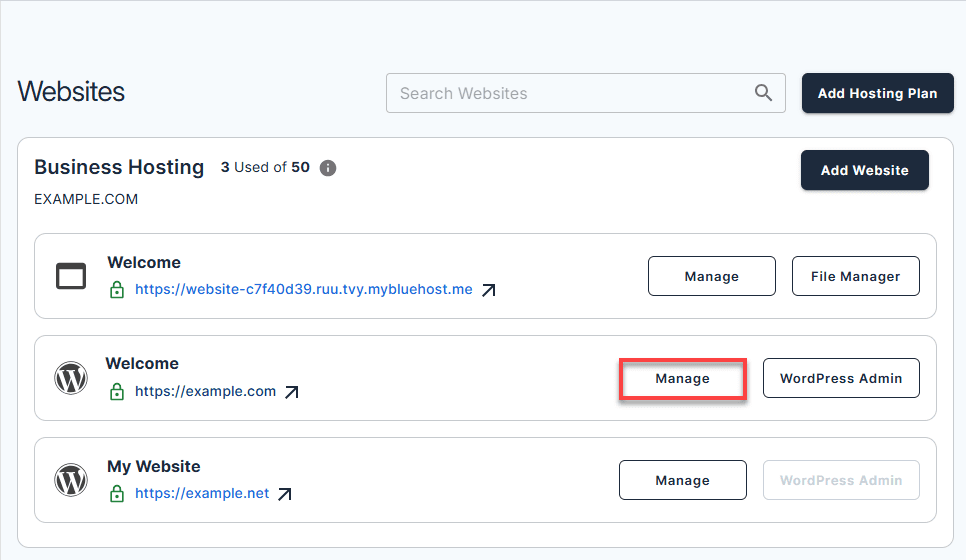
3. Find the website you want to manage and click Manage.
4. In the Overview section, click Databases.
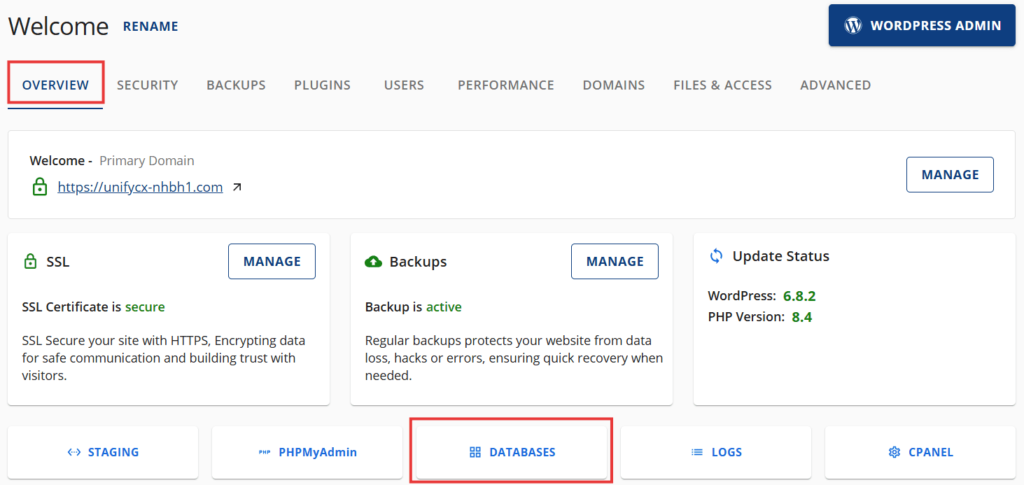
5. Open the Remote tab and click Add Host.
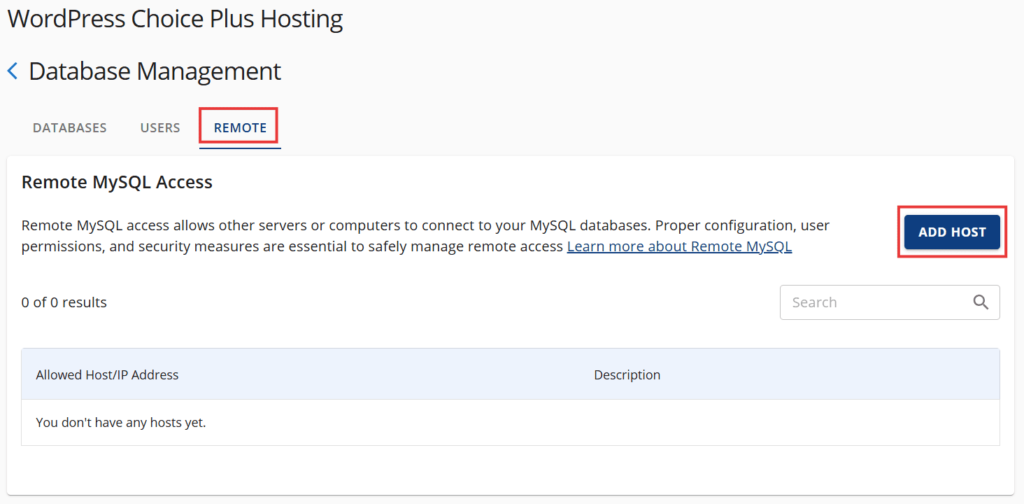
6. A pop-up window will appear. In the window, enter the IP address you want to whitelist. Add a short description to identify why the IP is being added. This step is optional.
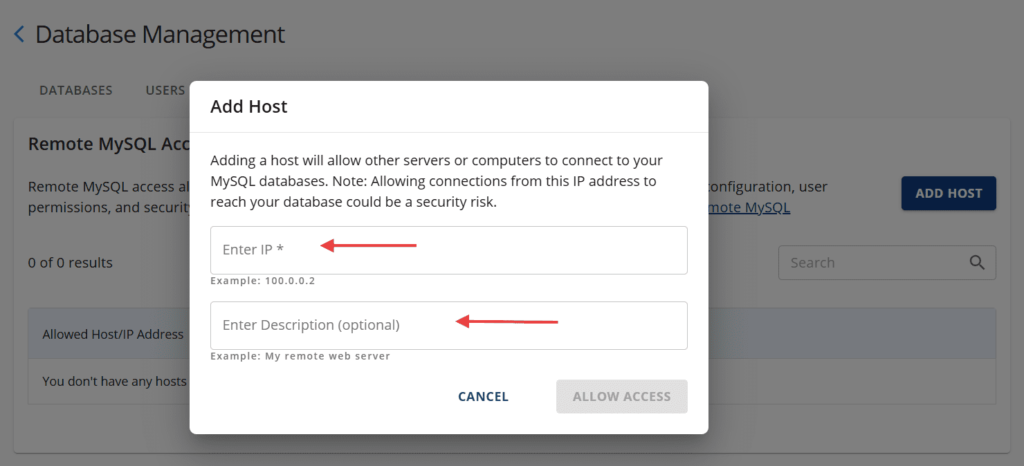
9. Click Allow Access to complete the process.
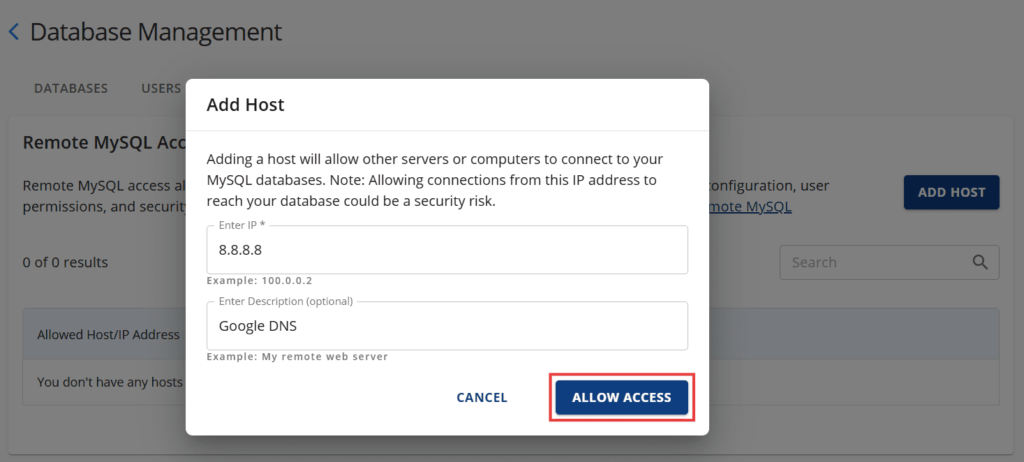
The IP address is now whitelisted and access is permitted. To proceed, you will need to identify your current IP address.
How to find your IP address
If you are not sure what your IP address is, visit: https://www.bluehost.com/ip
You may see an option called Class C. This allows all IP addresses within the first three octets, such as 192.168.0.*. Use this only when you need to allow a trusted IP range.
What to do if access is still blocked after whitelisting an IP address
Even after correctly whitelisting an IP address, access issues can still occur due to network changes, configuration delays or formatting errors.
When connectivity remains blocked, the problem is usually tied to how the IP address is assigned, cached or interpreted by security systems. The following checks help identify and resolve the most common causes of post-whitelisting access failures.
- Confirm IPv6 and IPv4 coverage. IPv6 addresses often require separate whitelist entries from IPv4 addresses, especially in modern dual-stack environments.
- Verify your current IP address matches the whitelisted entry exactly. IP address changes or dynamic IP assignment issues are the most common causes of post-whitelisting connectivity problems.
- Check for cached firewall rules or security policies. Restart firewall services or clear rule caches to ensure new whitelisting configurations take effect.
- Review IP range formatting and CIDR notation. Incorrect IP range formatting or subnet calculation errors can prevent successful whitelisting.
Common scenarios where IP address whitelisting is required
IP address whitelisting is commonly used to protect systems from unrestricted access by limiting connections to approved sources. Understanding the meaning of whitelist IP addresses helps clarify where this control is most effective and when it provides the greatest security value.
The following common scenarios show where whitelisting IP addresses is typically required and how this access control is applied across infrastructure, applications and third-party services.
1. Server and firewall access control
Servers often rely on network access control solutions that allow administrators to whitelist IP address entries at the firewall level. This ensures only trusted IPs can reach critical services while all other traffic is denied by default.
2. SSH, remote administration and internal tools
Remote access tools frequently require administrators to whitelist IP address sources before login attempts are accepted. Knowing how to whitelist IP address rules for SSH and internal dashboards helps prevent unauthorized access to administrative interfaces.
3. Database connections and restricted services
Databases commonly restrict connections via a whitelist of IP addresses. Only approved application servers or users can connect, reducing the risk of data exposure. In environments with multiple users, IP range whitelisting may be used to support controlled access without constant rule updates.
4. APIs, webhooks and third-party integrations
APIs often rely on IP whitelisting to verify trusted request sources. Third-party platforms may require you to provide a whitelist IP address or IP range before data exchange is allowed. This approach strengthens integration security and limits abuse.
5. Hosting control panels and SaaS dashboards
Control panels and SaaS dashboards frequently implement IP-based restrictions as part of broader network access control solutions. Applying IP whitelisting here reduces the risk of credential misuse and helps enforce access boundaries for sensitive configuration areas.
Best practices for IP address whitelisting
IP address whitelisting is most effective when it is applied with clear intent and ongoing oversight. Rather than treating whitelisting as a one-time security task, it should be managed as part of a broader access control strategy. The following best practices help ensure that whitelist IP addresses improve security without introducing unnecessary risk or operational complexity.
- Monitor access logs after implementing whitelisting changes. Track connection attempts to confirm legitimate users can access resources while unauthorized attempts are properly blocked.
- Keep whitelist IP addresses minimal and intentional to reduce the attack surface. Only add addresses that genuinely require access rather than pre-emptively whitelisting potential users.
- Use static IP addresses whenever possible for more reliable whitelisting. Dynamic addresses create maintenance overhead and can lead to connectivity issues.
- Review and remove unused IP entries regularly. Outdated whitelist entries may create access paths for compromised addresses or former users.
- Combine IP whitelisting with strong authentication and multi-factor authentication. Network access control solutions are most effective when layered with other security measures.
Final thoughts
IP whitelisting is most effective when it’s implemented as part of a layered security strategy rather than relied on as a standalone control. By understanding what IP whitelisting is and how a whitelist IP address works, you can make more informed decisions about who and what are allowed to access your systems, reducing unnecessary exposure while strengthening your overall security posture.
In Bluehost WordPress Hosting, IP whitelisting plays a strategic role in securing access at both the server and application levels. With direct control over database access rules, firewall configurations and IP-based restrictions, Bluehost enables a more intentional and adaptable approach to whitelisting, one that can evolve as network conditions and operational needs change.
When implemented thoughtfully and reviewed regularly, IP whitelisting becomes more than a security setting, it becomes a long-term control mechanism.
FAQs
The whitelist IP address meaning refers to creating an approved list of IP addresses that are allowed to access a system or network. Any IP address not included on the list is automatically blocked. This approach is widely used in network security consulting to control access to sensitive resources.
If your IP address changes, you will lose access to any system where that address was whitelisted. You must update the whitelist IP address settings with the new IP before access is restored. This situation commonly occurs when internet service providers assign dynamic IP addresses.
IP range whitelisting is more convenient but generally less secure than whitelisting a single IP address. Allowing a range increases the number of permitted addresses and expands the potential attack surface. When possible, a single whitelist IP address provides tighter access control.
Most whitelist IP address changes take effect immediately, especially at the firewall level. Some applications may require a service restart before the rules apply. In certain environments, caching or DNS behavior can cause short delays.
Write A Comment