All our blogs
Liked what you read, we think you might also like the following blogs
-
PuTTY PPK File: How to Create, Convert and Use It for SSH on Windows
Learn how to create, convert and use PuTTY PPK files for secure SSH access on Windows.
30 Mins Read -
How To Create a Print on Demand Store using WordPress in 2026
Build your print-on-demand store on WordPress today. Complete guide to setup, plugins and launching successfully.
16 Mins Read -
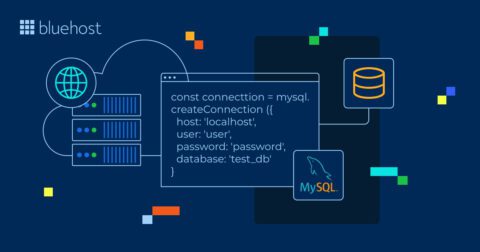
MySQL Connection Strings: Complete Guide for Developers (2026)
Learn about MySQL connection strings, syntax and how to use them in different scenarios.
16 Mins Read -

How to Hide Email Addresses from Bots and Spammers?
Learn effective methods to hide your email address for protection against bots and spammers.
14 Mins Read -
Virus Website Scan: Complete Vulnerability Protection Guide
Key highlights Your website could be silently infecting visitors right now without you even knowing it. Drive-by downloads are among…
13 Mins Read -
WordPress PHP Versions Explained: Best Practices, Comparisons & How to Choose the Right One
Learn how to choose, check and update the best WordPress PHP version for speed, security and stability.
11 Mins Read -

Bluehost Backups: Restore Your Site Using CodeGuard
Key highlights Your WordPress site is vulnerable to cyber attacks, server failures and plugin conflicts that can wipe out months…
12 Mins Read -
How to Create and Manage PostgreSQL Databases in cPanel?
Learn how to create and manage PostgreSQL databases in cPanel with clear steps, user setup, and best practices.
13 Mins Read -
How to Add SPF Record: Protect Your Domain Email
How to add SPF record: Simple Bluehost setup to authenticate emails, prevent spoofing, and boost inbox delivery with proper records…
17 Mins Read -
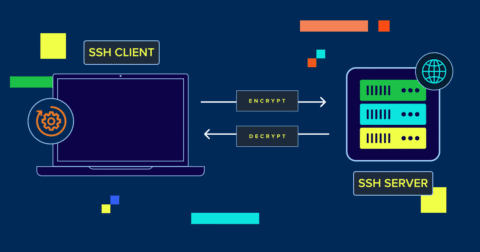
SSH Commands List: Master Secure Shell Basics
Essential SSH commands to connect securely, manage files, monitor performance and transfer data on Linux.
11 Mins Read -
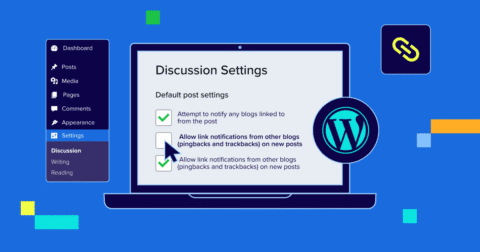
WordPress Pingbacks and Trackbacks: How to Disable Them
Learn what WordPress pingbacks and trackbacks are, how they work and if you should disable them.
9 Mins Read