Key highlights
- Learn the mandatory TLS versions required for PCI DSS compliance and payment security.
- Understand the timeline for implementing TLS 1.2 or higher across your payment infrastructure.
- Discover which legacy SSL/TLS protocols must be disabled to meet current standards.
- Explore practical configuration steps to secure your servers with compliant TLS settings.
- Know the common compliance pitfalls to avoid during your TLS migration process.
Are you confident your payment systems meet the latest security standards? For businesses processing credit card transactions, understanding and implementing PCI TLS requirements isn’t just a best practice. It’s a critical compliance requirement for protecting customer data and avoiding substantial penalties.
With the Payment Card Industry Data Security Standard mandating strict protocols for secure data transmission, staying compliant can feel overwhelming. This comprehensive guide breaks down everything you need to know about PCI TLS requirements. It covers fundamental concepts and compliance deadlines to practical implementation steps. You will learn how to ensure your payment infrastructure meets industry standards while safeguarding your business and customers.
Let’s get started.
What are the PCI and PCI Data Security Standards (DSS)?
The Payment Card Industry (PCI) is a collaborative effort between major credit card companies that establishes and maintains security standards for organizations that store, process or transmit credit card information.
PCI Data Security Standards (DSS) represent a set of comprehensive security requirements. It is designed to ensure that all companies accepting, processing, storing or transmitting credit card information maintain a secure environment.
These standards were created to reduce credit card fraud and protect sensitive cardholder data from security breaches through mandatory technical and operational requirements. PCI DSS applies to all entities involved in payment card processing, regardless of the number of transactions they handle annually. These entities include:
- Merchants
- Processors
- Acquirers
- Issuers
- Service providers
The standards encompass twelve main requirements covering areas such as network security, data protection, access control, monitoring and regular security testing to create a robust defense against data breaches.
Understanding PCI security standards
The Payment Card Industry Data Security Standard, commonly known as PCI DSS, represents a comprehensive framework of security requirements. It is designed to protect cardholder data during processing, storage and transmission. Established by major credit card companies including Visa, MasterCard, American Express and Discover. These standards apply to any organization that handles credit card information, regardless of size or transaction volume.
Within the broader PCI DSS framework, TLS requirements specifically address secure communication protocols that must be implemented to encrypt sensitive data as it travels between systems. The current PCI DSS version requires organizations to disable vulnerable protocols. Such as SSL and early TLS versions and to use TLS 1.2 or higher for all payment card data transmissions.
Understanding these standards is essential because non-compliance can result in hefty fines, increased transaction fees and potential loss of the ability to process credit card payments altogether.
For more information about the PCI requirements, check out PCI Compliance TLS Version Requirements.
Note: TLS 1.0 is now considered obsolete due to its security vulnerabilities, which could compromise cardholder data. For businesses to meet Payment Card Industry (PCI) compliance standards, TLS 1.1 or higher is required. Although TLS 1.1 still meets PCI standards, it is strongly recommended that TLS 1.2 or above be migrated for enhanced protection.
Understanding PCI security standards naturally leads to the technologies that enforce them, starting with Transport Layer Security (TLS).
What are Transport Layer Security (TLS) protocols?
Definition: TLS
Transport Layer Security (TLS) is a protocol that provides encrypted communication between a server and a client (such as a browser). It uses encryption keys from a Secure Socket Layer (SSL) certificate to secure sensitive data transmitted over the internet. Without TLS, hackers can easily intercept and steal valuable customer information, making it crucial for any business handling credit card payments or personal data.
What TLS protocols do?
TLS protocols are cryptographic standards that create secure, encrypted connections between browsers and servers.
They ensure sensitive information remains protected while moving across networks. TLS evolved from the older Secure Sockets Layer (SSL) protocol. Today, it is the industry standard for securing internet communication.
TLS is especially important for:
- eCommerce transactions
- Online payments
- Login credentials
- Personal and financial data
How does TLS protect data?
TLS works by creating an encrypted tunnel between the client and server.
This tunnel prevents unauthorized parties from intercepting or altering cardholder data during transmission.
TLS protection includes:
- Data encryption while in transit
- Server identity verification
- Message integrity checks
Why does TLS matter for PCI compliance?
TLS is fundamental to PCI compliance because it secures payment card data during transmission.
The protocol uses a handshake process to authenticate both parties and generate encryption keys. This establishes a secure session before any data exchange occurs.
Modern TLS versions include:
- Stronger cryptographic algorithms
- Improved key exchange methods
- Protection against vulnerabilities found in older SSL and TLS versions
How does TLS fit into PCI DSS?
TLS protocols are a fundamental security control within the PCI DSS framework. They specifically support Requirement 4, which mandates strong cryptography and security protocols. These measures safeguard cardholder data during transmission over open, public networks.
The PCI Security Standards Council requires organizations to use TLS 1.2 or higher for all connections involving cardholder data. At the same time, it prohibits vulnerable protocols such as SSL v2.0, SSL v3.0, TLS 1.0 and, in many cases, TLS 1.1.
This requirement means TLS compliance directly affects your overall PCI DSS certification status. Failure to implement proper TLS configurations can lead to automatic compliance failures during security assessments.
The standard also requires regular vulnerability scans and penetration testing. These tests verify that TLS implementations remain secure and properly configured across all payment processing environments.
In simple terms:
- PCI DSS defines the overall security rules
- TLS is one of the key technologies used to meet those rules
Failure to implement compliant TLS encryption can result in PCI non-compliance, even if other security controls are in place.
Now that TLS is clear, let’s see how it fits into the bigger framework of PCI compliance.
What is PCI compliance?
PCI compliance means following the Payment Card Industry Data Security Standard (PCI DSS) requirements. It shows that an organization has implemented proper security measures to protect cardholder data during payment processing.
What does PCI compliance involve?
Achieving compliance requires meeting all 12 core PCI DSS requirements, including:
- Maintaining secure networks
- Protecting stored cardholder data
- Using strong access control measures
- Regularly monitoring and testing security systems
These controls ensure payment environments remain protected against data breaches.
How do businesses validate compliance?
Organizations must confirm their compliance status using different validation methods. The approach depends on business size and transaction volume.
Validation methods include:
- Self-Assessment Questionnaires (SAQs) for smaller merchants
- Third-party security assessments for larger, high-volume organizations
The validation process typically involves:
- Vulnerability scans
- Penetration testing
- Documentation and security control reviews
These steps verify that required protections are properly implemented and maintained.
Why is PCI compliance critical?
Non-compliance can lead to serious consequences, including:
- Significant financial penalties
- Higher payment processing fees
- Possible termination of credit card processing privileges
Because of these risks, PCI compliance is a business requirement, not just an optional security improvement.
Note: Currently, TLS 1.0 no longer meets PCI compliance standards and businesses that continue to rely on this outdated protocol may risk losing their PCI compliance status, making it impossible to process payments securely.
With PCI compliance defined, the next step is understanding the specific TLS version requirements needed to meet these standards.
What are PCI TLS version requirements?
PCI TLS version requirements define how securely payment data must travel across networks. At their core, these rules ensure that any cardholder information moving between browsers, servers, APIs or payment systems is protected using modern, attack-resistant encryption.
According to PCI DSS, businesses handling payment data are expected to:
- Fully retire outdated encryption protocols such as SSL v2.0, SSL v3.0, TLS 1.0 and TLS 1.1
- Adopt TLS 1.2 or newer as the baseline for secure communication
- Configure systems to use strong cryptographic ciphers and disable weak or deprecated ones
- Apply these standards consistently across public websites, backend services, integrations, and internal data flows
The reason is simple: older TLS versions can be exploited using well-documented attacks, putting payment data at risk even if other security controls are in place. PCI TLS requirements shift encryption from a “nice-to-have” to a mandatory safeguard for trust, compliance, and breach prevention.
In practical terms, meeting PCI TLS requirements means your encryption is current, resilient and audit-ready, not stuck in the past.
Even when you use the correct TLS versions, configuration errors can still put PCI compliance at risk. Let’s see how you can avoid common implementation mistakes.
Common PCI TLS compliance mistakes to avoid
Even organizations with strong security practices often fall short on PCI TLS compliance due to configuration gaps and outdated assumptions. Below are the most common mistakes businesses make and why they matter:
- Assuming HTTPS automatically means compliance: HTTPS alone isn’t enough. If your site or API still allows TLS 1.0 or 1.1, it can fail PCI checks despite showing a secure padlock.
- Leaving legacy TLS versions enabled “just in case”: Many servers keep older TLS versions active for backward compatibility. Under PCI DSS, this is a compliance risk—even if stronger versions are also enabled.
- Overlooking non-browser traffic: PCI TLS rules apply beyond websites. Internal services, APIs, SFTP connections, admin panels and payment integrations are frequently missed during audits.
- Using weak or default cipher suites: TLS 1.2 is required, but pairing it with weak ciphers can still expose vulnerabilities. Secure TLS is about version + configuration, not version alone.
- Failing to document compensating controls: If a legacy system cannot support modern TLS, PCI expects documented risk analysis and compensating controls. Skipping this step can lead to audit failures.
- Not rechecking after updates or migrations: Server upgrades, CDN changes or hosting migrations can silently re-enable insecure protocols if TLS settings aren’t revalidated.
Avoiding these mistakes ensures your TLS setup is not only encrypted, but truly PCI-aligned, reducing audit friction, breach risk and last-minute compliance fixes.
Dodging these common mistakes is only the first step; let’s look at how to properly meet PCI TLS requirements.
How to meet PCI TLS requirements?
Meeting PCI TLS requirements is about maintaining a strong, consistent encryption posture across all systems that transmit cardholder data. Below is a clean, non-repetitive checklist with clear actions.
- Upgrade encryption protocols: Configure all payment-related systems to use TLS 1.2 or higher and fully disable SSL, TLS 1.0, and TLS 1.1 at the server, application, and network layers.
- Enforce strong cipher suites: Allow only PCI-approved, secure cipher suites and remove weak, deprecated, or anonymous ciphers to prevent downgrade and interception attacks.
- Protect all data transmission points: Apply TLS controls across websites, APIs, payment gateways, admin panels, internal services, and file transfers—not just customer-facing pages.
- Validate configurations regularly: Perform routine TLS scans and security testing to ensure insecure protocols are not reintroduced during updates, migrations, or infrastructure changes.
- Document legacy exceptions: Where modern TLS cannot be supported, conduct a formal risk assessment and record compensating controls in line with PCI DSS requirements.
- Monitor ongoing compliance: Run periodic PCI compliance scans and address findings promptly with your Compliance Scan Vendor to avoid audit failures.
- Maintain client-side compatibility: Ensure browsers and client applications support modern encryption standards, as outdated software may block secure TLS connections.
By following these steps, organizations can move beyond basic encryption and achieve sustainable, audit-ready PCI TLS compliance without last-minute fixes or hidden risks.
Beyond configuring TLS versions, proper SSL certificate deployment is essential for maintaining PCI-compliant encryption. Let’s see how it helps.
SSL Certificates and PCI TLS Compliance
TLS encryption depends on SSL certificates to establish secure connections. Without a valid SSL certificate, encrypted communication required for PCI compliance isn’t possible.
Most modern hosting environments simplify this process by including SSL certificates by default.
How can Bluehost help?
Bluehost includes free SSL certificates with all hosting plans, making it easy to enable encrypted connections right from the start. For businesses handling sensitive transactions or higher traffic volumes, Bluehost also offers a premium SSL certificate plan that provides enhanced validation and stronger trust signals.
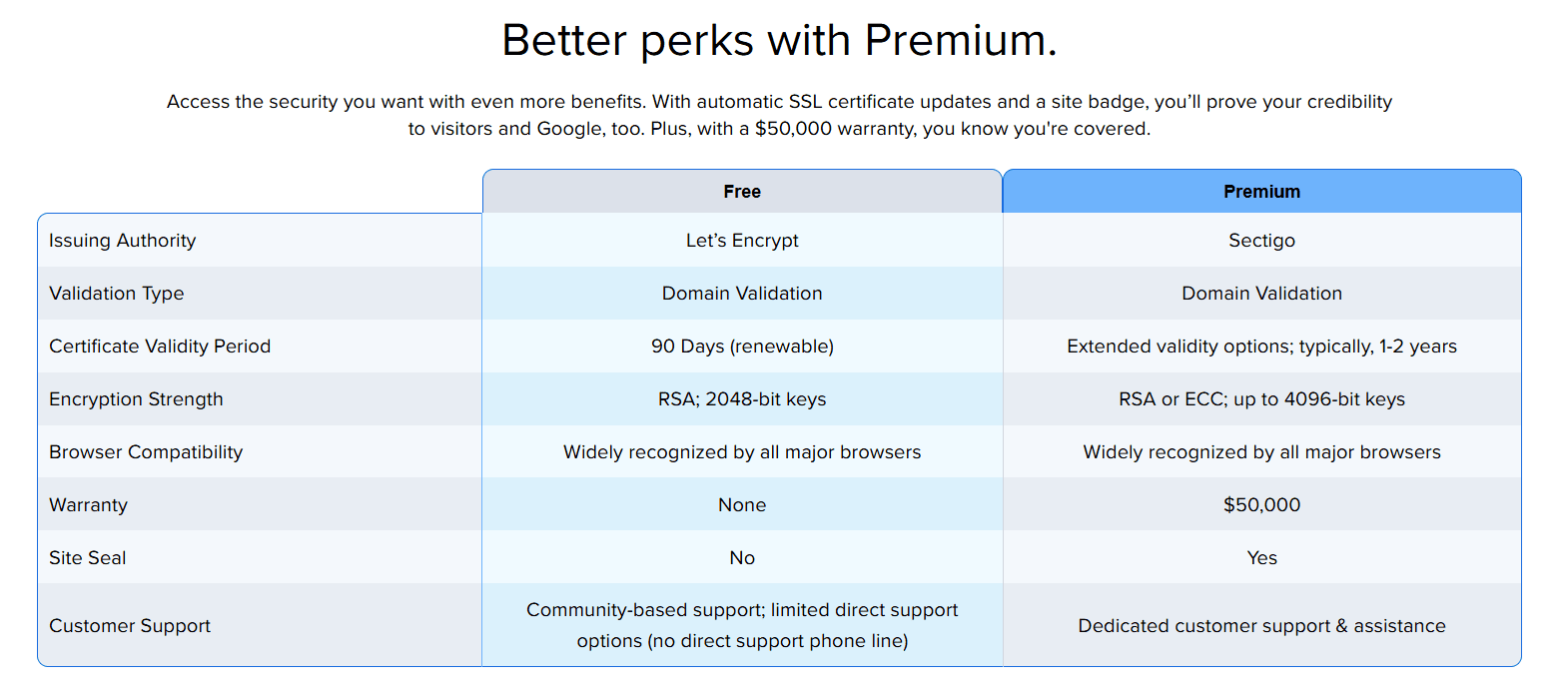
This flexibility allows businesses to:
- Meet PCI TLS requirements easily
- Improve customer trust with secure connections
- Scale security as business needs grow
Secure your website with Bluehost SSL today and make PCI TLS compliance effortless from day one.
Final thoughts
Staying compliant with PCI TLS requirements doesn’t have to feel overwhelming. By now, you understand the critical security protocols needed to protect customer payment data and maintain your business’s credibility.
The good news? You don’t have to tackle this alone. Having the right SSL certificate in place is your first line of defense against compliance violations and security breaches.
Ready to secure your website and meet PCI TLS requirements effortlessly? Explore Bluehost’s SSL certificate solutions today and give your customers the protection they deserve while keeping your business compliant.
FAQs
PCI DSS mandates TLS 1.2 or higher for encrypting cardholder data during transmission. Older protocols like SSL and TLS 1.0/1.1 are prohibited due to security vulnerabilities, ensuring robust protection for payment card information across all network connections.
TLS 1.0 and 1.1 contain known vulnerabilities that attackers can exploit to intercept sensitive payment data. PCI Security Standards Council retired these protocols to enforce stronger encryption standards and protect cardholder information from evolving cyber threats.
All organizations handling payment card data must use TLS 1.2 or TLS 1.3 immediately. The PCI DSS deadline for disabling older TLS versions passed in 2018, making current compliance mandatory for maintaining payment processing capabilities.
Use SSL Labs’ free SSL Server Test tool or command-line utilities like OpenSSL to verify your server’s TLS configuration. Check that TLS 1.2 or 1.3 is enabled and older protocols are disabled to meet PCI DSS requirements.
Non-compliance with PCI TLS requirements can result in hefty fines, loss of payment processing privileges, increased transaction fees, and potential data breach liability. Payment card brands may also impose additional security audits and monitoring requirements on your business.
While TLS 1.3 offers enhanced security, PCI DSS currently accepts TLS 1.2 as the minimum requirement. However, implementing TLS 1.3 provides stronger encryption, improved performance, and better future-proofing against emerging security threats for payment environments.
Self-signed certificates don’t meet PCI DSS requirements for production environments. You must use certificates from trusted Certificate Authorities to establish verified, encrypted connections that protect cardholder data and maintain industry compliance standards.

Write A Comment